Organizations: Managing Operators, Controller APIs & Licensing¶
The organization section can be reached by clicking the Organization link in the header.
Note
The currently logged-in user must have Controller Administrator access in order to see the Organizations link in the header. The initial user in the organization gets this access by default. See Access Control for more information.
SwiftStack Controller Operators¶
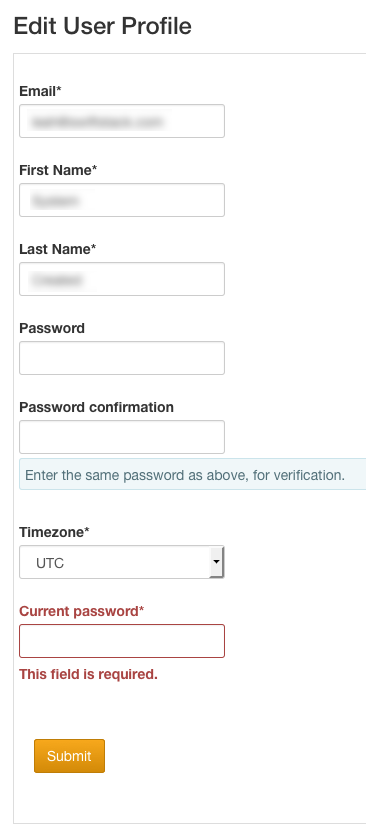
Controller users / operators (of all access levels) can view their own profiles by clicking on their username in the header.

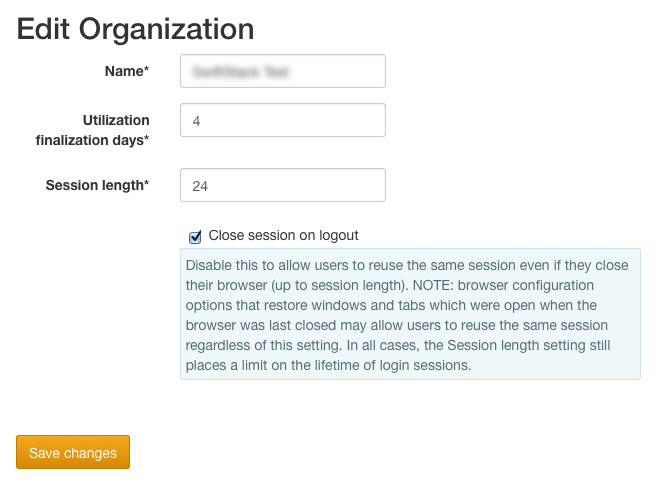
Depending on the user's roles, they may be able to click through to edit the organization name and user roles.
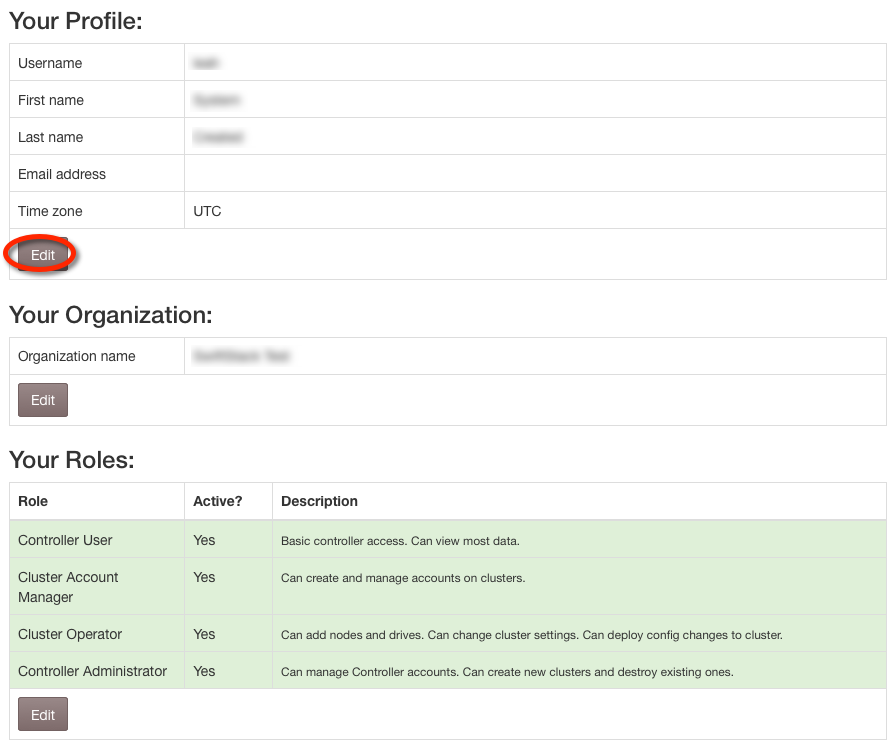
All controller users can click edit on the top section and edit their personal details including time zone. Password confirmation will be required, even if the password isn't being changed.
SwiftStack Controller Users and Access Control¶
Customer Portal Registration & Controller Organization Creation¶
When someone registers on the SwiftStack Customer Portal (https://portal.swiftstack.com/customer/signup/ ), they are creating both their Customer Portal account and setting the organization name which is used across all SwiftStack systems. In particular it is used to create an organization with that name on SwiftStack Controller As-a-Service.
Upon registration, a portal user can then invite the first administrators to their SwiftStack Controller As-a-Service organization. The newly invited admins will receive an email and follow the instructions to complete their registration on SwiftStack Controller As-a-Service. Once they are registered on SwiftStack Controller As-a-Service, they can create the first cluster and ingest the first node.
Note
For SwiftStack Controller On-Premises installations, only one organization is permitted, and the initial user localadmin is created during installation. Users who will be able to upgrade the controller should be registered separately on both the Customer Portal and the controller.
Inviting Users to the Organization¶
If your organization has multiple users who will be able to access the same collection of clusters and nodes, then there are two ways to invite more users:
- Additional administrators can be invited via the Customer Portal using the same method as inviting the initial user (See instructions above) or an administrator can invite a new user from the controller organization itself (See instructions below).
- Additional users (not admin) can be invited from the controller organization via an invitation from the controller interface (See instructions below).
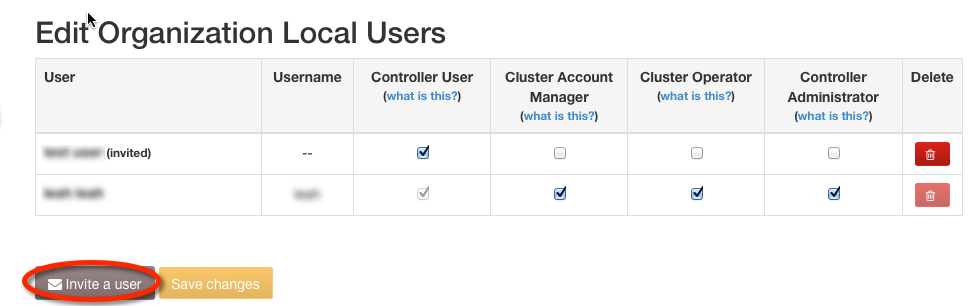
The Users tab on the Edit Organization page lists the users currently a part of the organization. Users can be deleted using the Delete button in that user's row. Invitations to join the organization may be issued by clicking on the Invite a user button.
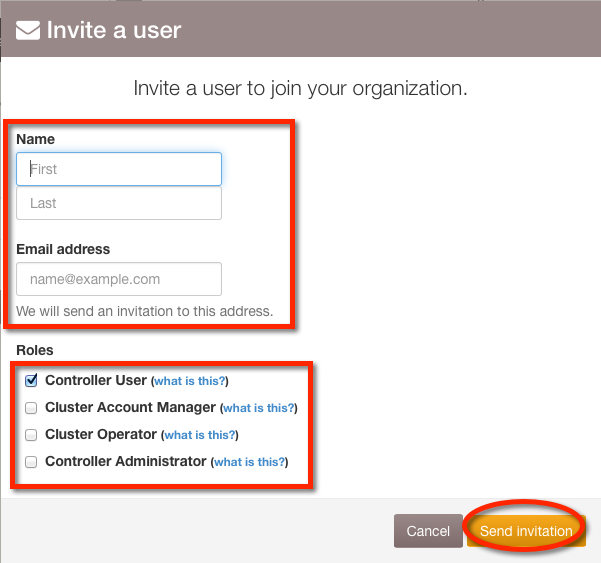
The invitation dialog asks for the new user's name, email, and permissions.
Note
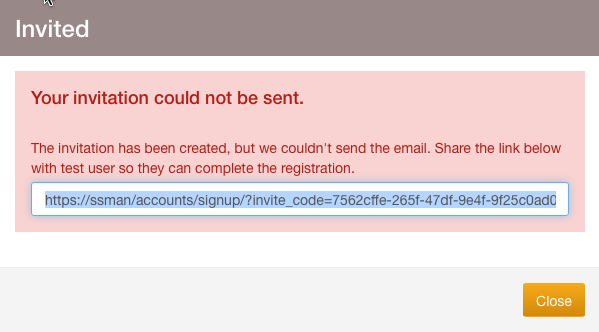
If there is an error sending the email, a message will appear which contains the invitation sign-up link.
Access Control¶
The controller offers 4 access control levels. Note that controller roles are "additive", not "heirarchical", so for example, a user with the Controller Administrator role does not have basic access unless the user also has the Controller User role. This distinction is most important when using LDAP to authenticate and authorize controller users to a SwiftStack Controller On-Premises controller.
Controller User¶
Users with the Controller User role have the most basic access and can see but not edit the data.
Cluster Account Manager¶
Users with the Cluster Account Manager role may create, delete, and change passwords for Swift Storage Accounts on the cluster(s).
Cluster Operator¶
Users with the Cluster Operator role can add nodes and drives, change cluster tuning settings, modify middleware, and push configuration to clusters.
Controller Administrator¶
Users with the Controller Administrator role can create, delete, assign permissions to Controller User accounts, create API Keys, and create and delete clusters.
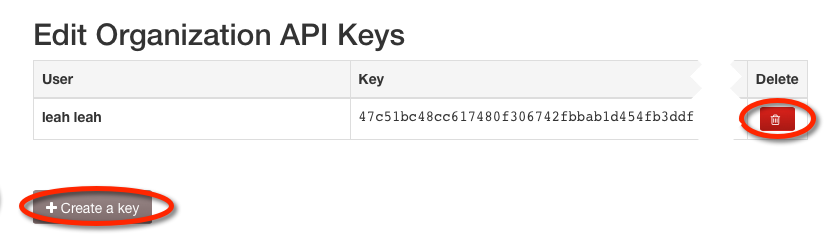
API Keys¶
API Keys are required for use of the SwiftStack Controller's RESTful API (see SwiftStack Controller API Documentation for more information). The API Key tab on the Edit Organization page lists existing API Keys and allows them to be deleted. Click the Create a key button and select a user who does not already have a key to create a new API Key.
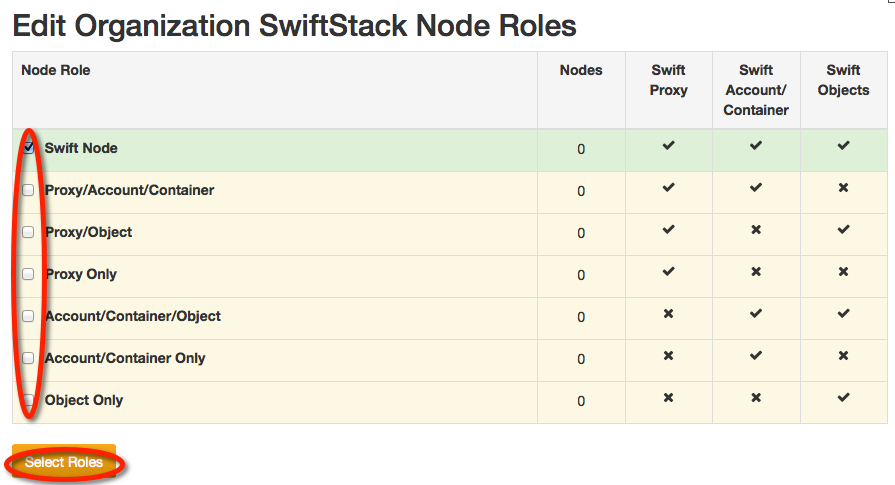
Cluster Node Roles¶
Node roles dictate which storage services should run on the nodes within a cluster. Node roles are initially assigned at ingest, but may be changed later from the Manage Node page's Change Role tab.
By default, only the All Swift Services role is enabled. It runs all Swift services.
You can allow more roles to appear as options at ingest by checking the boxes on the left then clicking Select Roles. Note that you cannot disable a role that is currently in use.
Note
The currently logged-in user must have Controller Administrator access in order to enable and disable node roles. The initial user in the organization gets this access by default. See Access Control for more information.
Note
Node role options apply across all clusters for your organization.
Proxy Services¶
Proxy services handle incoming AWS S3 and Swift API requests. They receive a request, examine the URL on the object and then determine which storage node to connect to. Additionally, they handle:
- Timestamps
- Load balancing (if running the SwiftStack load balancer)
- Failures
- SSL termintations
- Authentication
Storage (Account/Container & Object) Services¶
At the heart of a cluster are storage nodes running storage services. Primarily these services include:
- Fielding incoming requests from the proxy services, by storing and serving accounts, containers, and objects.
- Replication for accounts, containers, and objects.
- Auditors for accounts, containers, and objects.
- Updaters to keep containers and accounts up-to-date.
Since account and container data are accessed much more frequently, those services are isolated as their own tier. This allows you to select servers with faster disks and network interfaces to host account and container data, while using cheaper hardware to host object data.
File Access Services¶
A node role may also be created for the purposes of providing SMB or NFS access to a configured storage account.
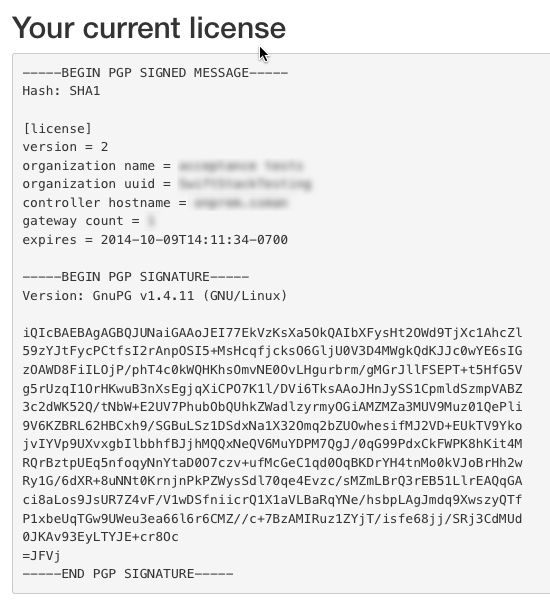
Licensing¶
Please contact sales@swiftstack.com with the information provided on this page to get a license.
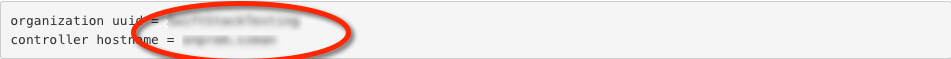
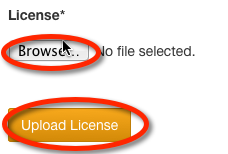
Once you receive the license, upload it here.
Your valid license will appear on this page.